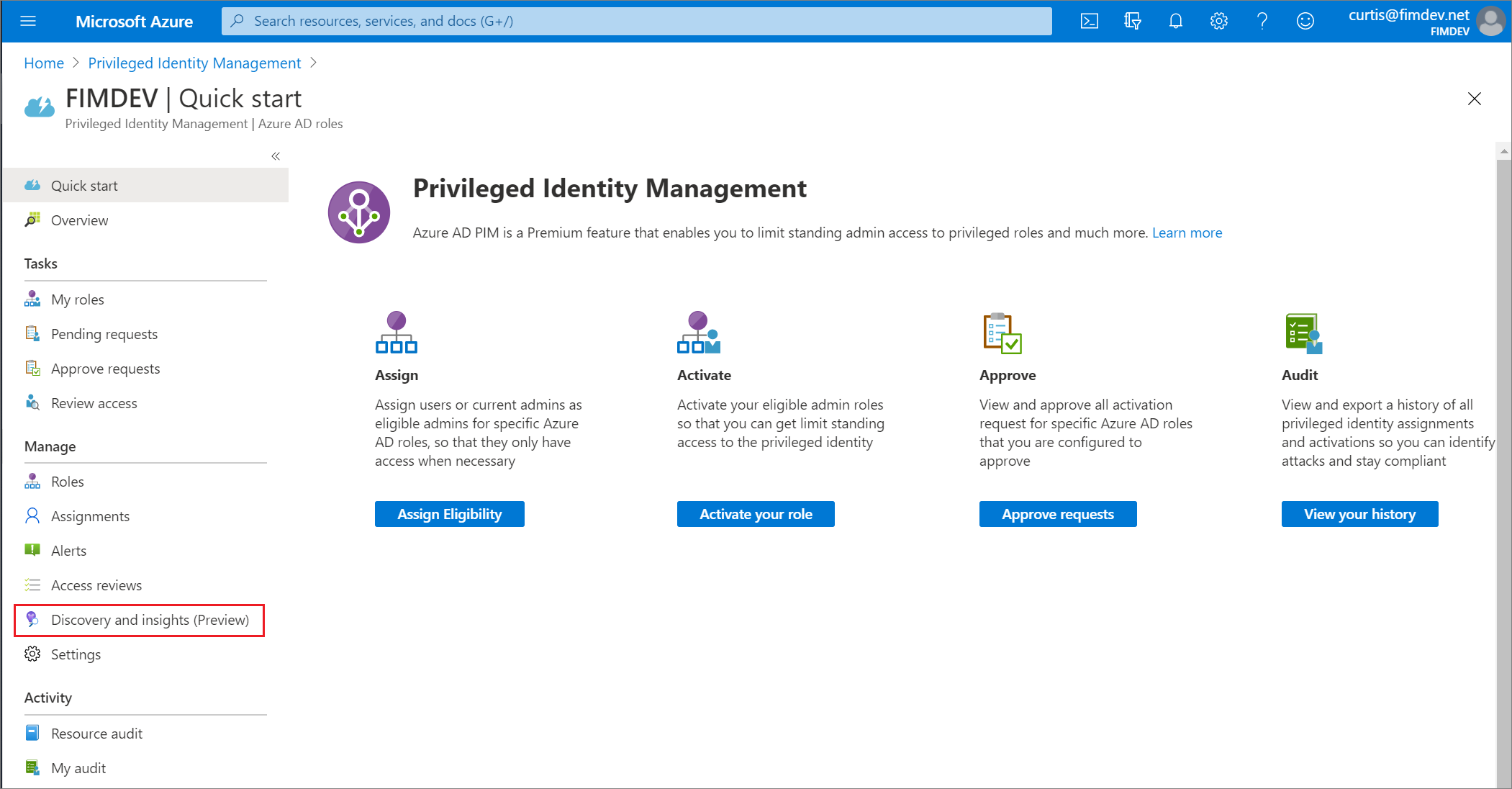
Azure AD roles Discovery and insights (preview) in Privileged Identity Management former Security Wizard - Microsoft Entra | Microsoft Learn

Privileged identity management software solutions for enterprise|PIM suite - ManageEngine Password Manager Pro

Privileged Identity Management (PIM) overview - Azure Video Tutorial | LinkedIn Learning, formerly Lynda.com

Privileged Identity Management (PIM) Solution Market Booming at a CAGR of +29% by 2030 |Centrify, BeyondTrust, Broadcom





.png)